Schlagwörter
Aktuelle Nachrichten
America
Aus Aller Welt
Breaking News
Canada
DE
Deutsch
Deutschsprechenden
Global News
Internationale Nachrichten aus aller Welt
Japan
Japan News
Kanada
Karte
Karten
Konflikt
Korea
Krieg in der Ukraine
Latest news
Map
Maps
Nachrichten
News
News Japan
Polen
Russischer Überfall auf die Ukraine seit 2022
Science
South Korea
Ukraine
Ukraine War Video Report
UkraineWarVideoReport
United Kingdom
United States
United States of America
US
USA
USA Politics
Vereinigte Königreich Großbritannien und Nordirland
Vereinigtes Königreich
Welt
Welt-Nachrichten
Weltnachrichten
Wissenschaft
World
World News
4 Kommentare
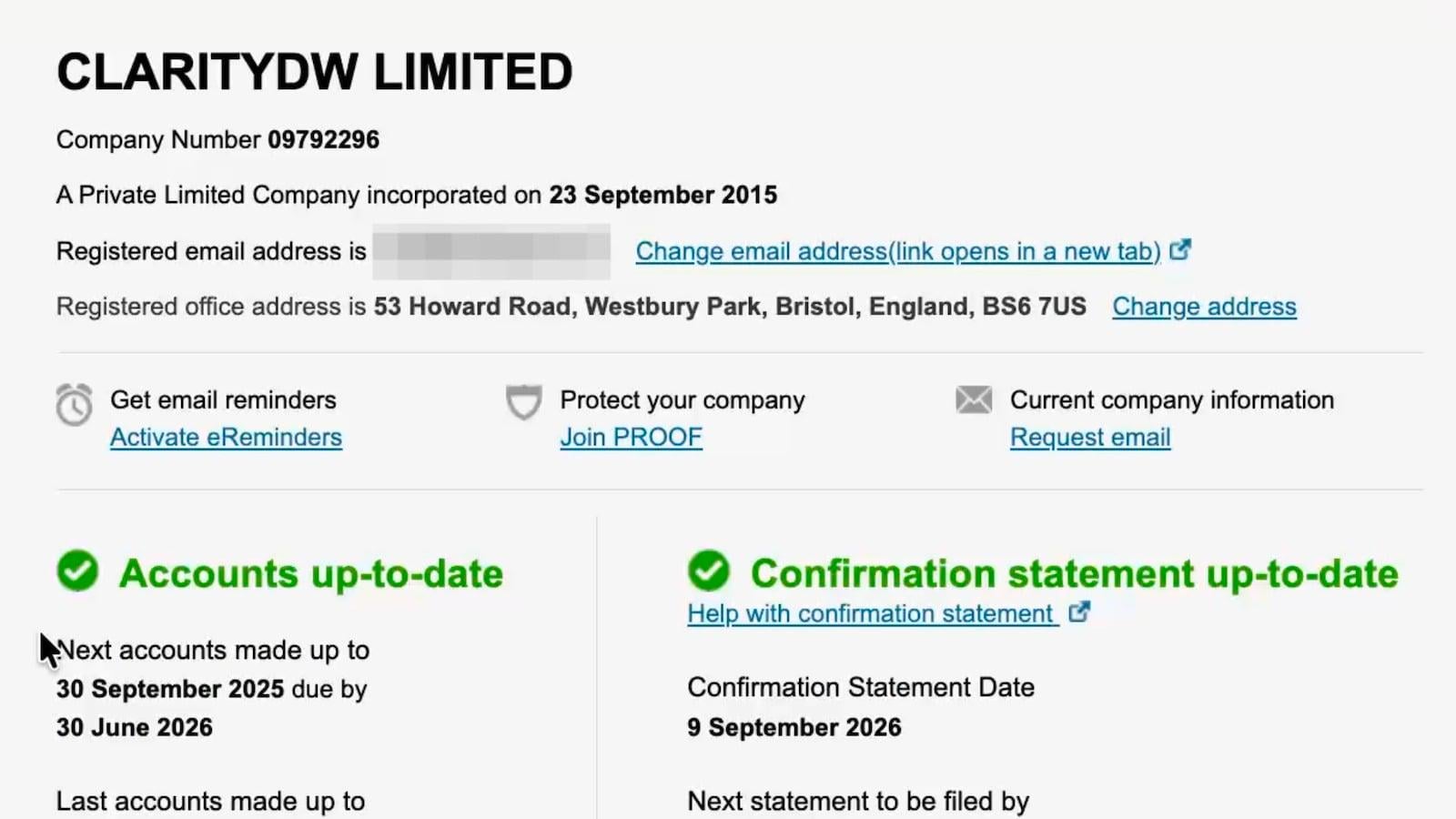
This seems remarkably similar to the issue Lloyd’s Bank had the other day.
As I read through the description I got that sinking feeling in my stomach only a dev gets when he *finally* gets to the bottom of a bug and it some code that has ‚TODO‘ next to it.
I suspect to get round the security usually in place, you have a cookie that temporarily turns you into the other company. Sounds like dev debug / testing code that got left if with the intention to do the real work later.
And as any dev will tell you, later never comes.
Oh wow this is bad. Especially as there’s probably no easy way to tell what is a „real“ edit and what is one done while in the wrong session like this.
I don’t understand why you would give a session authentication rights before you enter the verification code, unless your system is a horrible mess. It shouldn’t be possible to access that data yet.
Mind you the 2FA in my company’s process was originally a bit like this because you have to store which user you are trying to 2FA for somewhere, and it was patched on as a later feature. Making sure we caught all the ways you could „log in“, not complete 2FA and then try to access content directly was a big pain. It’s much better now after the auth code got rewritten.
At least they shut the website down asap.
Sounds like code that overwrote session information or something. Failing to sanitise or store those credentials separately.
I’d have thought this be something that should have been caught by testing, given how many people click back on things
Or maybe it was for testing and somehow ended up in prod, which then makes you wonder why processes didn’t catch it